By Robbin Laird
To achieve the kind of agility and decisive effect which 5th generation maneouver can achieve requires a significant re-focus on the nature of the C2 and ISR infrastructure.
Such an evolved infrastructure enables the legacy and new platforms which are re-shaping capabilities for the combat force to be much more capable of operating across the full spectrum of crisis management.
In today’s world, full spectrum crisis management is not simply about escalation ladders; it is about the capability to operate tailored task forces within a crisis setting to dominate and prevail within that crisis.
If that stops the level of escalation that is one way of looking at it.
But in today’s world, it is not just about that but it is about the ability to operate and prevail within a diversity of crises which might not be located on what one might consider an escalation ladder.
They are very likely to be diffuse within which the authoritarian powers are using surrogates and we and our allies are trying to prevail in a more open setting which we are required to do as liberal democracies.
This means that a core legacy from the land wars and COIN efforts needs to be jettisoned if we are to succeed – namely, the OODLA loop.
This is how the OODA loop has worked in the land wars, with the lawyers in the loop, and hence the OODLA loop.
The OODA loop is changing with the new technologies which allow distributed operators to become empowered to decide in the tactical decision-making situation.
But the legalistic approach to hierarchical approval to distributed decisions simply will take away the advantages of the new distributed approach and give the advantage to our authoritarian adversaries.
But what changes with the integrated distribute ops approach is what a presence force can now mean.
Historically, what a presence force is about what organically included within that presence force; now we are looking at reach or scalability of force.
We are looking at economy of force whereby what is operating directly in the area of interest is part of distributed force.
The presence force however small needs to be well integrated but not just in terms of itself but its ability to operate via C2 or ISR connectors to an enhanced capability.
But that enhanced capability needs to be deployed in order to be tailorable to the presence force and to provide enhanced lethality and effectiveness appropriate to the political action needed to be taken.
This rests really on a significant rework of C2 in order for a distributed force to have the flexibility to operate not just within a limited geographical area but to expand its ability to operate by reaching beyond the geographical boundaries of what the organic presence force is capable of doing by itself.
This requires multi-domain SA – this is not about the intelligence community running its precious space- based assets and hoarding material.
This is about looking for the coming confrontation which could trigger a crisis and the SA capabilities airborne, at sea and on the ground would provide the most usable SA monitoring.
This is not “actionable intelligence.”
This is about shaping force domain knowledge about anticipation of events.
This requires tailored force packaging and takes advantage of what the new military technologies and platforms can provide in terms of multi-domain delivery by a small force rather than a large air-sea-ground enterprise which can only fully function if unleashed in sequential waves.
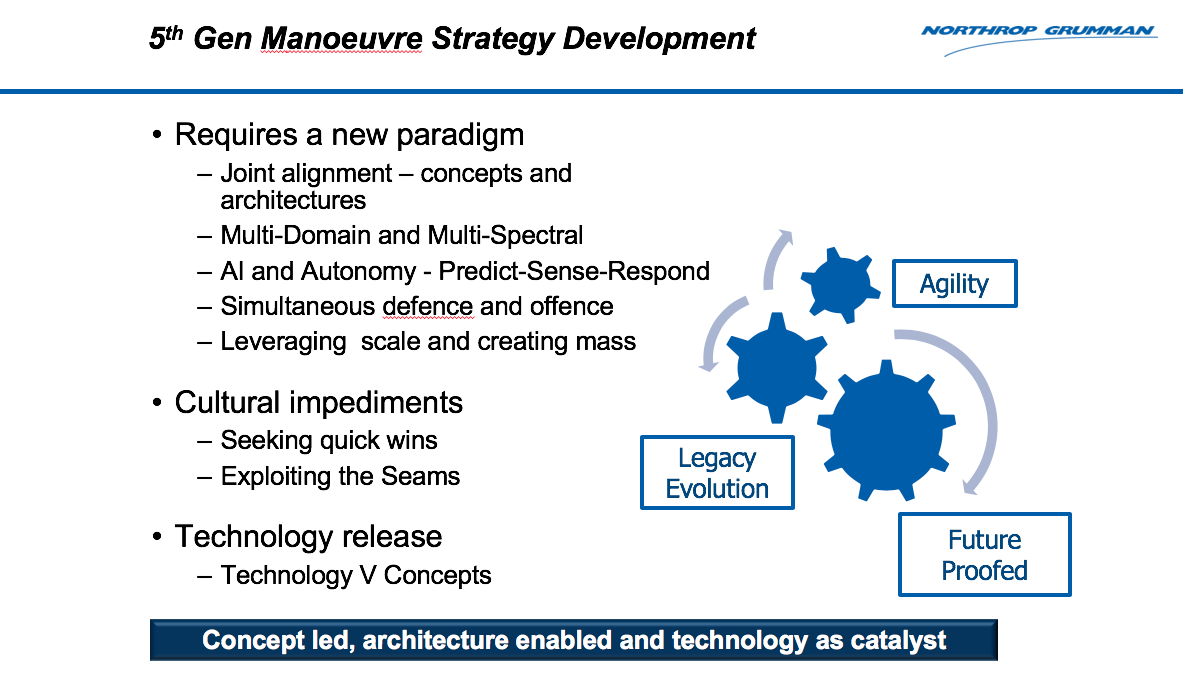
The focus on the requirements for fifth generation maneouver at the Williams Foundation seminar underscored several key aspects of how to achieve the outcome of a tailored force which could achieve sufficient effects to operate and determine outcomes across the spectrum of crisis management.
Getting the Right Piece of Information to the Right Shooter, the Right Effector, the Right Sensor, at the Right Point in Time
Air Vice Marshal Chris Deeble, now retired and now head of Northrup Grumman in Australia, provided a perspective based on his unique experience working the fifth generation transition in the RAAF. He has worked on the Wedgetail, the tanker, and the F-35 programs, and based on a decade of extensive experience bringing new capabilities to the RAAF and the ADF, he is well positioned to suggest ways ahead with regard to the build out of a fifth generation maneouver force.
The core target which needs to be achieved in order to enable, empower and further develop the fifth generation force was identified by Deeble as follows: “Getting the right piece of information to the right shooter, the right effector, the right sensor, at the right point in time.”
He argued that such an outcome cannot occur by happenstance but must be the focus of attention from the outset. “It must be architected.”
Deeble underscored that “we need to focus on information management as a maneuver force capability. It is not just about the platforms, but the information enabling the joint force to operate as a fifth generation maneouver force.”
He further argued that for such a capability to become a dominant reality will require “future proofing the force” by having an evolving but guiding architecture which is based on operational experience and open ended to innovations.
But it is crucial that such innovation is done through evolving adaptations from operational experience, rather than long lists of requirements keeping industry outside of the ongoing conceptual rethinking.
“We have not yet achieved critical mass for the kind of collaborative efforts which can achieve this outcome.”
But clearly this is the means through which the ongoing future proofed architecture can be shaped and implemented by the innovations being delivered by the combat force operating throughout the spectrum of conflict management.
Rethinking the Nature of Networks
When describing C2 and ISR or various mutations like C4ISR, the early notions of C2 and ISR seen in both air-land battle and in joint support to the land wars, tend to be extended into the discussions of the C2 and ISR infrastructure for the kill web or for force building of the integrated distributed force.
But the technology associated with C2 and ISR has changed significantly throughout this thirty year period, and the technology to shape a very different kind of C2 and ISR infrastructure is at hand to build enablement for distributed operations.
As Marja Phipps of Cubic Mission Solutions highlighted with regard to the evolving approach to building out C2 and ISR networks:
“Earlier we built a dedicated single network connection for a specific task, such as providing targeting information to the platforms involved in a specific operation.”
The “networked” force was built around platforms that would use networked information to create desired and often scripted events.
But the C2 and ISR revolution we are now facing is reversing the logic of platforms to infrastructure; it is now about how flexible C2 and ISR interactive systems can inform the force elements to shape interactive combat operations on the fly.
That is, the new capabilities are enabling tactical decision making at the edge and posing real challenges to traditional understandings of how information interacts with decision making.
It is about learning how to fight effectively at the speed of light in order to achieve combat dominance.
And these new capabilities are providing a real impact on force development, concepts of operations and force training as well.
“With the new technologies and capabilities, we are now reusing networks for multiple purposes and making sure that they can adapt to the changing con-ops as well.”
“We are seeing integration of the networks and the integration of the information management services and then the dual nature of the applications on top of those integrations.
“Rather than building a single purpose intel common operating picture, we are now capable of building an integrated intelligence and battlespace management common operating picture for the use of the combat forces engaged in operations.”
In other words, “we are building an adaptable network of networks. In traditional networks, when data is brought in from a dedicated system, it needs to be repurposed for other tasks as needed.”
At the seminar, AIRCDRE Leon Phillips, OAM Chief Information Officer Group, provided a very comprehensive overview to the kind of changes, both evolutionary and revolutionary, which networking was undergoing as the infrastructure of the ADF as a fifth generation force.
According to AIRCDRE Phillips:
Modern, 5th generation defence forces, will need to be competent across the continuum of conflict, supporting times of political tension through to high-end peer to peer warfighting.
This left and right of arc has the potential to leave us conflicted with choice over exactly what our data and network needs are. Notwithstanding, technology growth is leading to a greater array of more complex sensors and shooters, dispersed across the battlefield.
We face the threat of faster, more agile hypersonic threats and the proliferation of disruptive technology offered by cheaper drones as well as attacks on our networks.
For us to be effective we need to ensure our systems are well connected, through robust, multi-pathed networks and that we are capable of operations despite degraded networks.
Data exchange between tactical and strategic networks offers us competitive advantage and we need to recognise the merging and synergistic nature of both. We are benefiting through our investment in high-end warfighting technology however need to think more deeply about the information exchange between these and our CONOPS so we make the best investments and tradeoffs in a fiscally constrained environment.
Finally, we must invest more heavily, both intellectually and financially in the development of weapon systems and C2 systems that we develop as they give us control in how we bind and glue our tactical systems together, ensuring our ecosystem is optimised.
He argued that the investment piece clearly needs to be aligned with what Deeble was calling for in terms of architectures which can deliver the kind of sovereign capability which Australia needs for its fifth- generation force but capable of being interoperable with allies and partners as well.
This is not Costco buying where we leverage US economies of scale by buying in packs of 6. Like all good investment portfolios, there should be some money slated for high risk, high return ventures. The real Jericho challenge is to convince the Investment Committee and Government of this.
Noting the volume of data we capture and the likelihood of constrained data paths, I suggest this data analytics needs to be at both the tactical and strategic level to ensure only data of value is kept and shared.
For instance, you can collect a lot of imagery on a maritime patrol flight but how much is useful?
Processing at the tactical edge to extract more immediate value and sharing only what is of value is paramount. Opportunities exist to use our developed and controlled technologies such as our converged deployable and embedded networks to be the hub of this effort. It’s the applications that are hosted here that we need to invest in with a tighter coupling of strategist, warfighter, delivery agency and industry.
At the strategic level there will be an abundance of data. Data from allied sources and data collected over days, months and years. Combing through the data, perhaps more slowly than at the tactical edge, can offer us early queues on our adversary’s intent.
Earlier on I mentioned the geopolitical landscape and the murky nature of modern conflict. Data analytics at this level may need to expand beyond traditional military sources, depending on the circumstances.
How much social media and public information would we also be interested in?
Having an agility to respond and evolve our analytics given the strategic circumstance we find ourselves in is important.
Again, investment in Australian owned and developed data systems allows us this flexibility.
Enhancing the Capability of the ADF to Contribute to Full Spectrum Crisis Management
The COS of the RAAF, Air Marshal Mel Hupfeld, provided the final presentation at the Williams Foundation Seminar. In his presentation, he embraced the earlier discussions on the C2, ISR, network development assessments, but underscored how he saw such efforts reshaping the capabilities of the ADF and its role for the nation.
Clearly, a fifth-generation force “Will necessarily require robust redundant ITC systems capable of handling an exponential growth in data generation accompanied by exponential increases in processing power and speed.”
Certainly, as the ADF enhances its network capabilities to deliver a more integrated force, it will be more capable of multi-domain integrated operations.
But for the Air Marshal, we needed to think beyond narrowly considered kinetic or warfighting impacts of such a capability.
“The multi-domain approach should not be limited to thinking about combat scenarios. We should use a multi-domain approach across the spectrum of operations to shape our thinking about how to generate access, presence, influence, deterrence, denial….”
In effect, he argued that force integration was not an end in of itself but a means of expanding Australian influence in the region and its ability to more effectively defend Australia’s interests.
Enabling fifth generation maneouver means that the ADF can expand its role and utility for the Australian government to expand its impact and influence throughout the region and globally.
In short, although the discussion of C2, ISR and networking can get terribly technical, the ground truth is that these are means to enhance an operational force’s capabilities which, in turn, enhance its utility to the nation and to the ability of the national leadership to achieve the effects, politically and diplomatically they seek.
The featured graphic was taken from Air Vice Marshal (Retired) Chris Deeble’s Presentation
AIRCDRE Leon Phillips, OAM Chief Information Officer Group’s Presentation to the Williams Foundation Seminar
AIRCDRE Phillips Brief to Williams Foundation 20191024 V3Also, see the following articles which highlight the Williams Foundation Seminar held on October 24, 2019:
Defending Australia: The Role of Fifth Generation Manoeuvre Capabilities
Strategic and Operational Changes: Australia Facing an Evolving APR